Another Day Another Vulnerability Revealed in Intel CPU
Instead of waiting for the exploit to be found and announced by any third party organization, Intel has announced a new vulnerability in the CPUs dubbed TSX Asynchronous Abort (TAA). Apart from this vulnerability, Intel has also disclosed a bug called Jump Conditional Code (JCC), fixing which will entail performance impact.
TAA are an extension to the x86 instruction set architecture that adds hardware transactional memory support to improve performance of multi-threaded software
TAA is again a speculative execution attack that may allow malicious codes to locally execute code to extract sensitive data. In order to be safe, Intel recommends disabling hyper threading. These affects the new Intel CPUs including Whiskey Lake, Cascade Lake, and Coffee Lake R processors that support its Intel TSX technology.
What is Speculative Execution?
Speculative execution is a technique used by modern CPUs to speed up performance. The CPU may execute certain tasks ahead of time, “speculating” that they will be needed.
Then there is (JCC) erratum affecting CPUs based on the Skylake architecture and above. Intel has issued microcode update to fix the issue but with a performance penalty of 4%.
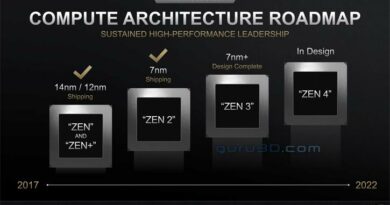
This is the kind of news Intel would like to avoid as AMD has already announced it’s new zen 2 line up (Ryzen 9 and Threadripper). Intel might want to fix the bugs in future CPU but that means ceding more performance.
- Titan Fall(ter): Intel’s Stumble an Analysis - August 5, 2024
- AMDs Radeon Future Looks Bleak After RDNA 5 - May 1, 2024
- Kinect 2- Right time to use A.I. in Nextgen Consoles? - April 30, 2024